7 Real-World Data Storage and Management Threats that can be Mitigated through NetApp Training
The worst kind of data security threat is the one where there's no way to recover or restore data. Such a loss of sensitive or crucial data asset can bring the company down. Therefore, backup and restore are two crucial aspects of data security that an organization can make the most of, through NetApp training. The training ensures your workforce learns proven skills in positioning efficient backup and recovery solutions. Moreover, they have a better understanding of assessing customer requirements with regards to storage as well as implementing a system that reduces the chance of data storage and management threats.
With NetApp certification, your team learns key backup and recovery terminology and technologies to be able to implement effective concepts that mitigate the risk. Moreover, they can offer NetApp disaster recovery offerings as they are able to identify threat and risk at a more personal level.
Real-World Data Storage and Management Threats
NetApp training prepares individuals and teams to establish multi-layer security solutions to mitigate data storage and management threats for secure operations. The first step to any prevention plan is to identify threats and vulnerabilities. Naturally, training enables the security control team to become more cautious about it.
Here are the top threats that can easily be taken down by a team of trained employees.
Excessive Privileges
When employees are given database access privileges that are not relevant or required by their job functions, this creates vulnerability of abuse. This is particularly very important for databases holding sensitive business information. When granting access, it is important to take the job functions of the employees into account to find out if they need that privilege. The organization must take a proactive approach in this regard and immediately cut access of an employee they do not consider suitable for the specific privilege. Similarly, the organization must also update the access based on the change in roles within the organization and when an employee switches job. In some cases, users with legitimate privilege may also abuse it.
Injection Attacks
Two major attacks fall in this category. The SQL injection attack is one where the attackers target a traditional database system, while NoSQL injection attacks target big data platforms. However, contrary to the prior understanding, even big data solutions are under threat to SQL injection attacks. The ultimate point of these attacks is to get unrestricted access to an overall database.
Malware
There are various types of malware security threats that organizations are susceptible to. It's also one of the most common data storage and management threats that an organization has to deal with. The main purpose of this cybercrime is to steal sensitive data and use it against the organization for an unauthorized purpose or to ask for ransom against the key code. The malware attack usually effects through infected devices used by legitimate users.
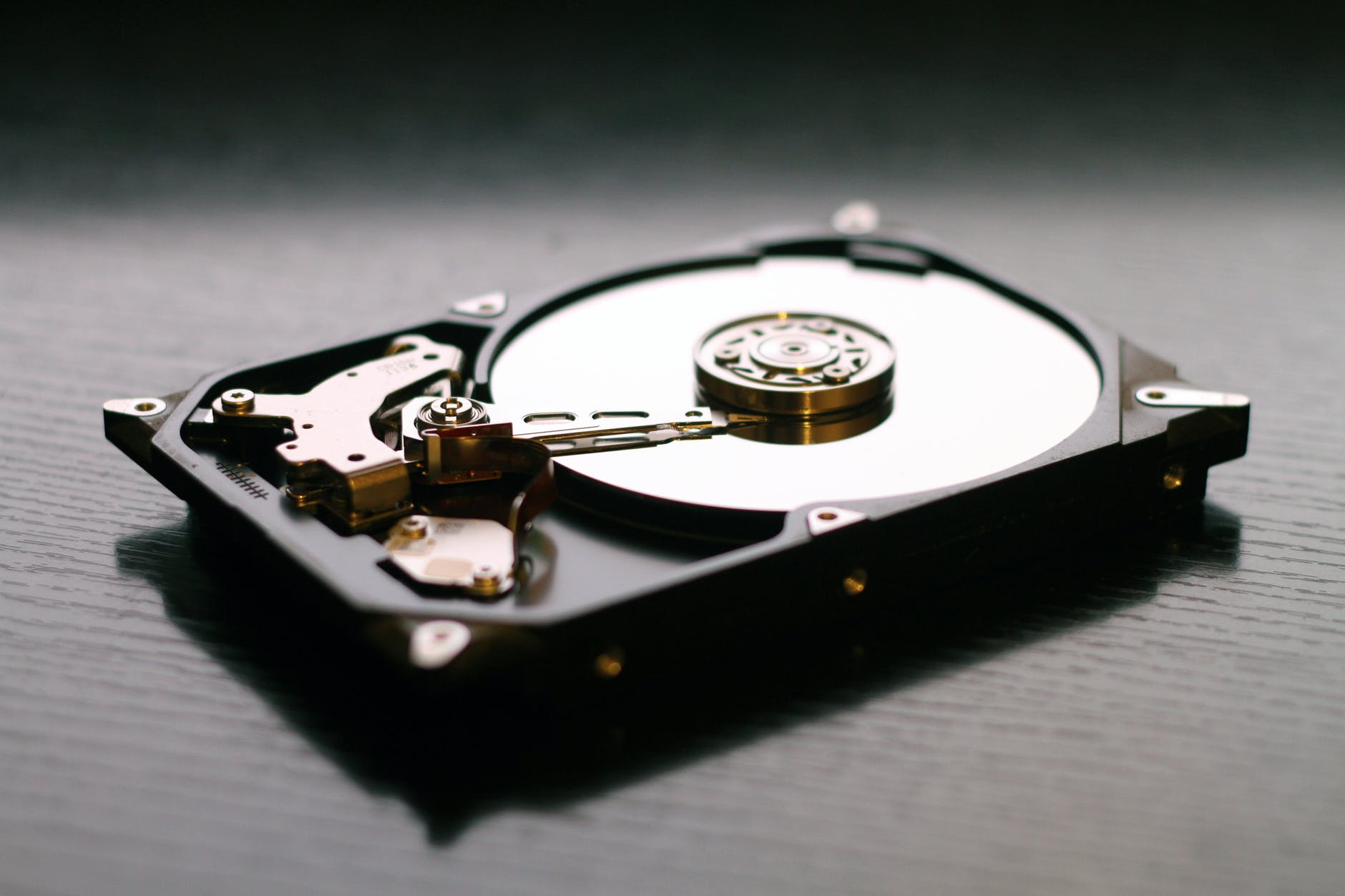
Storage Exposure
The security teams usually have their full emphasis on the security of actual databases. Backup storage media is usually at high risk due to non-protective measures. Since attackers and cybercriminals are becoming more tech-oriented and sophisticated, they usually cause the breach involving theft of backup tapes and disks for the database. Moreover, failure to monitor and audit the activities of admin, most sensitive information is put at risk. It is crucial to take appropriate measures to not only protect the original data but also the backup copies. Additionally, training encourages the responsible teams to monitor not only the database but the highly privileged users to ensure they are in sync with the data security best practices.
Vulnerable Databases
Patching databases can be a hectic process that could take up to a month to complete. This time can put the system at risk and make databases vulnerable and easy to exploit. Unpatched databases are easy to exploit. Even though they may not hold the entire information, attackers can make use of the configuration parameters and default accounts it holds. This is the number one reason why organizations often fail to maintain database configuration even when patched. Common problems include mounting backlogs, high workloads, time-consuming and complex requirements for testing patches, and challenges related to finding a window for taking the system down for maintenance.
Unmanaged Data
Just like data storage, data management also plays a crucial role in maintaining database security. Most organizations still struggle to maintain their databases with accurate information on inventory and other critical data objects. With upgrades and tons of new information, it is easy to forget about certain databases, which may still contain sensitive information that remains unmanaged. Naturally, this information is exposed to threats and does not have proper controls or permissions to stay protected.
The Humans
Last but not the least, this one's the most prominent real-world threat that NetApp can help with. Studies show how more than 30% of data breaches involve human error or negligence. Lack of training, proper education, and expertise required to enforce policies implement security controls, and conduct threat and breach response processes are the root cause of why there's a risk of data breach.
Multi-Layer Security Solution
In addition to all that NetApp training can offer, here are a few more multi-layer security solutions they can ensure implementing for maximum results.
- Assessing the databases in detail to identify vulnerabilities, sensitive information, and compromised endpoints.
- Better management control over user access privileges, and removing dormant users.
- Encrypting databases and archiving external data.
- Automating regular auditing with protection platform and database.
- Monitoring database activities and usage patterns to detect data leakage in real time.
- Monitoring to identify unauthorized SQL, system attacks, protocol, and big data transactions.
- Training other departments and teams on risk-mitigation techniques to avoid cyber threats of different nature - especially phishing attack.
- Information users about best practices around password management, email usage, and internet access.
Allowing your team of trained individuals to set up a breach response plan will help reduce the impact of harm. The key is to understand what you are putting at stake and how having a more informed approach can prevent data storage and management threats.
