Connect with our experts for counseling on your next step to succeed in your career. Start your 30-day free trial to gain access to over 900 self-paced courses.
Subnet vs VLAN: Everything You Need to Know
At the highest level, both VLAN and subnet are similar in such a manner that they are dealing with a segment or partition of a network. Although, VLAN’s are those which are the data link layer (OSI layer 2) constructs. On the other side, subnets are considered as network layer (OSI layer 3) IP constructs, and they also address another kind of concern within a network. However, it is usual practice for creating a personalized association among a subnet and a VLAN. It is a fact that both of them are independent at layer 3 and layer 2 and are constructing further scalability while they design the network.
OSI Model Layers
As soon as we discuss subnet or VLAN, we are concisely covering the OSI Model. The Open Systems Interconnection (OSI) is a model which is conceptualizing the mode of computing functions. It’s a seven-layer model that is utilized, like a tool to trace flowing of the data on the network. This kind of model is usually breaking down by the protocol is utilized for communicating. As it is suggested by the name, layer 1 is a physical level where the processing of the data initiates. Layer 7 (app layer) is the top layer where protocols, such as HTTP and telnet, are communicating. Apart from this, every other thing, from initiating the request of data to get the internet falls among those two layers.
Start your 30-day free trial to get your hands on in-demand IT certifications. Connect with our experts to learn more about our IT courses.
What Is VLAN?
VLAN owns similar characteristics, like physical local-area network. However, it is allowing for the devices to connect altogether with no trouble, even though in case they aren’t linked on a similar network switch. Separating the ports by VLAN grouping is separating their traffic, in the same manner, to connect devices towards the individual and different switch. VLANs offer a much higher level of security along with great scalability for relatively little cost.
Network designers who obtained Cisco training are making use of VLANs to segmenting traffic for matters just like network management, flexibility and safety. Switches will not (or else, as a minimum should not) bridge Internet Protocol traffic among VLANs, as doing this would interrupt the reliability of the VLAN broadcast field. So, in that case, if a single VLAN would have cooperated in some way, the remainder of the network wouldn’t be delayed. The power of the service schemes would enhance traffic on the VLANs for actual time (VoIP) or else low latency necessities (SAN).
If we don’t have VLAN, then the switch would be considered the entire device on a switch to get in a similar broadcast field. Thus, VLANs would fundamentally generate several layer 3 networking on an individual physical substructure. Let’s suppose the DHCP server plugged in and switching it would offer any of the hosts on such kind of switch, which is arranged for the DHCP. By making use of VLAN, the network would be splitting up so few of the hosts would not utilize that DHCP server and would attain link-local address or else attain address from another kind of DHCP server.
What Is Subnet?
Any of the Internet Protocol addresses would rationally split (sub-netting) into two portions: host identifier and routing/network prefix. Network devices belong to subnet sharing usual routing/network prefix within their IP addresses. The networking prefix is determined by relating bitwise and an operation among Internet Protocol addresses and a mask of the subnet (typically 255.255.255.0). However, utilizing a sample address of 192.168.5.130, the networking prefix is 192.168.5.0, whereas the host identifier is 0.0.0.130.
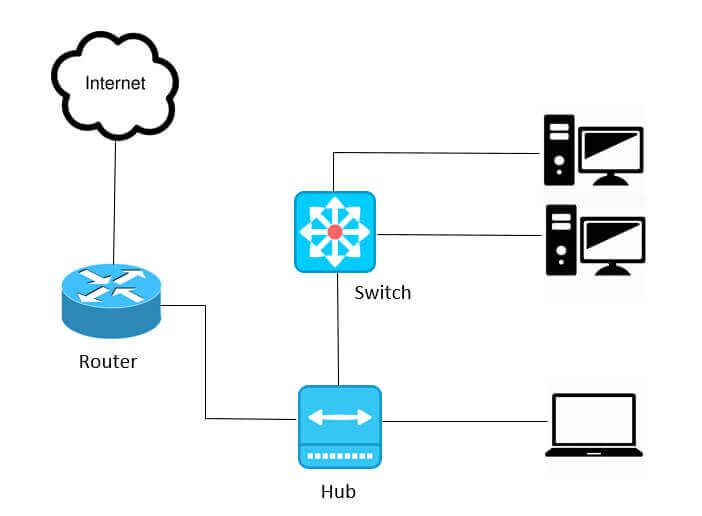
Traffic is swapped or else routed among sub-networks through the routers (multiple innovative switches also consist of the functionality of the router). While subnet/routing prefixes of resource address, as well as the address of the destination, are not the same. A router is establishing a physical/ logical boundary among subnets.
It might also optimize routing efficiency or else have benefits in the networking management once sub-networks are administered by other kinds of inner groups. Subnets would be organized rationally in a hierarchical manner, dividing the networking address of an organized space in a tree such as routing structure.
Subnet vs VLAN
You would own a single physical network along with configuring more than two consistent networks by merely conveying other kinds of subnets, such as 192.168.1.0 and 192.168.0.0. On the other side, both of the subnets are transmitting the data via a similar switch. Traffic going via switch would be viewed by all kinds of hosts. Though, it does not matter in which subnet they are on. The outcome is security is less, and there would be not as much bandwidth accessible, because the entire traffic is making use of a similar backbone.
In its place, one would generate VLAN for every logical network. The availability of bandwidth for every VLAN or else for the logical network would not share anymore. All the same, security is optimized since the switch, which gets connected to every VLAN network and wouldn’t enable traffic for crossing among VLANs. In general, VLANs are considered a great choice of selection for numerous apps, together with audio. However, there are certain situations where subnet makes sense. These are the major reasons:
- Justifying performance issues as LANs would not scale them indefinitely. Extreme broadcasts or else overflowing of the frames to unidentified destinations would restrict their scalability.
- The need to restrict or control the movement of traffic among hosts at layer 3. In thise case, a person is interested in controlling Internet Protocol traffic among the hosts, instead of criticizing the issue at layer 2, you would think about subnet as well as add firewalls or routers along with A-C-Ls among subnets.
Wrapping Up
The VLAN is working at Ethernet level (layer 2) - whereas the subnet is working at the Internet Protocol level (layer-3). It is essential to be aware of this dissimilarity to avoid misconfigurations and safety oversights. In the meanwhile, VLAN would upsurge communication among devices on LAN by turning it, like they are fundamentally physically linked all together. However, a subnet generates several hosts to restrict the volume of data that is routed toward that host, enabling you to get ready for the potential development. Like we stated earlier, you own a restricted number of Internet Protocol addresses on any of the subnet. It’s usual to own one VLAN to one subnet, offering you an additional layer of safety at both of the layers.
